Luxembourg Financial Regulatory News:
The CSSF issued an urgent warning regarding a cybersecurity breach targeting the Axios library, a widely used tool for handling web requests. Malicious actors infiltrated the supply chain by hijacking developer accounts to insert a harmful dependency known as plain-crypto-js. This intrusion poses severe risks to financial entities, including credential theft and unauthorized remote code execution. Organizations that updated their software during the specific infection window on March 31, 2026, are advised to isolate affected systems and perform a total security reset. Additionally, the regulator mandates that all impacted institutions officially report the incident under established ICT guidelines.
Executive Summary: Supply Chain Attack Targeting Axios NPM Packages
On April 3, 2026, the Commission de Surveillance du Secteur Financier (CSSF) issued a critical alert regarding an active supply chain attack targeting the Axios HTTP client library, a fundamental component in many software architectures. Threat actors successfully compromised maintainer accounts to inject a malicious dependency, plain-crypto-js, into specific versions of the Axios package.
The compromise occurred during a narrow window on March 31, 2026, specifically between 00:21 and 03:25 UTC. Any systems that performed an npm install or updated Axios to versions 1.14.1 or 0.30.4 during this timeframe must be treated as fully compromised. The potential impact includes remote code execution (RCE), credential theft, and lateral movement within the affected Information System. Supervised entities are required to perform immediate remediation and notify the CSSF of the incident under applicable regulatory frameworks.
Overview of the active supply chain attack targeting Axios NPM
The attack targeted the Axios NPM package by compromising the accounts of authorized maintainers. This unauthorized access allowed attackers to inject a malicious dependency into the build pipeline.
Malicious Component Details
The primary vehicle for the attack is the injection of the following dependency:
- Malicious Package: plain-crypto-js
- Specific Version: 4.2.1 (though any version should be treated with suspicion)
Affected Axios Versions
The threat specifically impacts two versions of the Axios library:
- Axios 1.14.1
- Axios 0.30.4
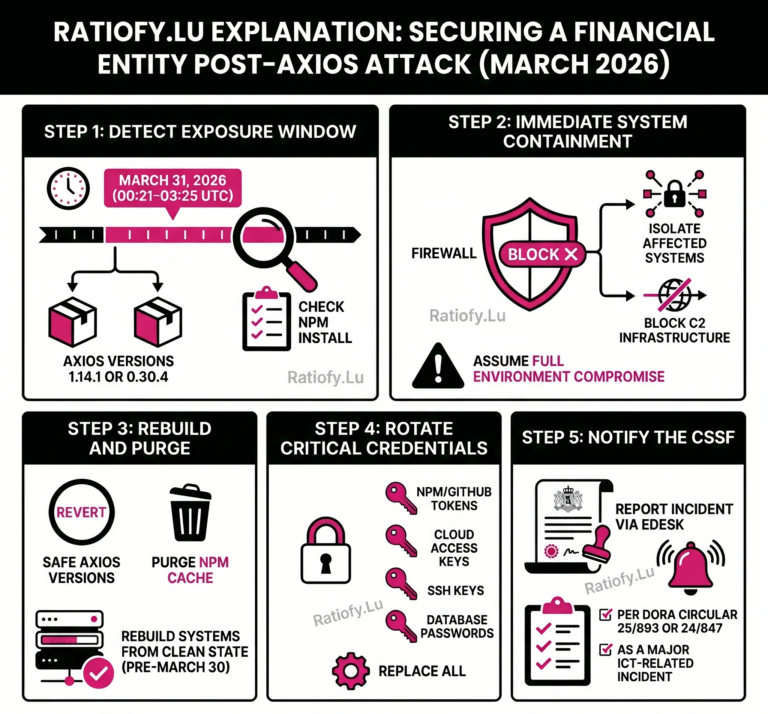
| Step | Description | Key Requirements | Mandatory Remediation Action |
| Step 1: Detection and Inventory | Supply chain attack involving a compromised build pipeline to inject a malicious dependency (plain-crypto-js). | Identify if Axios is used in the environment and if npm install/update was executed between 00:21 and 03:25 UTC on March 31, 2026. | Check for Axios package usage; treat systems as compromised if malicious versions were installed during the breach window. |
| Step 2: Containment and Isolation | Mitigating risk of Remote Code Execution (RCE), credential theft, and lateral movement from compromised dependencies. | Immediate severance of affected systems from the network to prevent further spread or data exfiltration. | Immediately isolate the affected system from the network and block Command and Control (C2) infrastructure. |
| Step 3: Identity and Access Remediation | Compromise of maintainer accounts leading to the potential theft of secrets, tokens, and access credentials. | Invalidate and replace all secrets that could have been exposed during the system compromise to prevent unauthorized access. | Rotate all credentials (secrets, tokens, keys) and ensure future hardening using Multi-Factor Authentication (MFA). |
| Step 4: Recovery and Eradication | Restoring system integrity by removing malicious payloads and reverting to verified, secure codebases. | Complete removal of the malicious dependency and restoration of the environment from a verified clean backup. | Rebuild system from a clean state (pre-March 30, 2026), revert to a safe Axios version, and purge NPM cache. |

Risk Assessment of the active supply chain attack targeting Axios NPM
Because Axios is central to many software architectures, a compromise of its build pipeline provides attackers with significant leverage. The CSSF identifies the following primary risks:
- Remote Code Execution (RCE): The ability for attackers to execute arbitrary commands on the host system.
- Credential Theft: The potential harvesting of sensitive tokens and keys.
- Lateral Movement: The use of the compromised system to navigate and infect other areas of the internal Information System.
Identification and Compromise Window of the active supply chain attack targeting Axios NPM
The CSSF has defined a specific “compromised window” for this incident. Organizations that executed package management commands during this time are at the highest risk.
| Date | Time Window (UTC) | Action Leading to Likely Compromise |
| March 31, 2026 | 00:21 to 03:25 | npm install or update to Axios 1.14.1 or 0.30.4 |
Critical Note: Entities that installed these versions within this window should assume their systems are fully compromised and that the malicious payload has been pulled into their environment.
Mandatory Remediation Actions of the active supply chain attack targeting Axios NPM
The CSSF recommends that all supervised entities using the Axios package implement a comprehensive remediation strategy. The following actions are considered the minimum required response:
- System Isolation: Immediately isolate any system identified as affected to prevent further spread or data exfiltration.
- Credential Rotation: Rotate all secrets and credentials, including:
- NPM and GitHub tokens
- Cloud access keys
- SSH keys
- Database access keys
- System Restoration: Rebuild the affected systems using a known clean state from before March 30, 2026.
- Network Security: Identify and block Command and Control (C2) infrastructure.
- Version Control: Revert to a known safe version of the Axios package.
- Cache Management: Purge the NPM cache to ensure no malicious artifacts remain.
- Ongoing Surveillance: Implement continual monitoring for further signs of compromise.
- Future Hardening: Strengthen security posture for the future, specifically by implementing Multi-Factor Authentication (MFA).
Regulatory Reporting Requirements after the active supply chain attack targeting Axios NPM
As this supply chain intrusion involves unauthorized malicious access, it is classified as a major ICT-related incident. Under CSSF regulations, supervised entities are mandated to submit notifications regarding this breach.
Notifications must be filed according to the relevant framework:
- Circular CSSF 25/893 (DORA): For entities falling under the Digital Operational Resilience Act.
- Circular CSSF 24/847: For other applicable supervised entities.
Scope of Impact under the active supply chain attack targeting Axios NPM
The CSSF indicates that this alert and the subsequent remediation requirements are relevant for a broad spectrum of professionals and institutions, including but not limited to:
- Banking and Credit: Credit institutions and mortgage credit intermediaries.
- Investment Services: Investment firms, fund managers, and investment vehicles.
- Crypto and Digital Assets: Crypto-Assets Service Providers (CASPs), Virtual Asset Service Providers (VASPs), and Issuers of Tokens.
- Payment and Infrastructure: Payment institutions, electronic money institutions, AISPs, and Central Securities Depositories (CSDs).
- Specialized Professionals: Specialized PFS, Support PFS, and Crowdfunding service providers.
- Data and Audit: Data Reporting Service Providers (DRSPs) and the Public Oversight of the Audit Profession.
This news related to Active supply chain attack targeting Axios NPM can be considered beneficial under CSSF-Circulars, Central Securities Depositories (CSDs) News, Credit Institutions News, Crowdfunding service providers (CSPs) News, Crypto-Assets Service Providers (CASPs) and Virtual Asset Service Providers (VASPs) News, Data Reporting Service Providers (DRSPs) News, EU Regulations, Explanation, IFMs (AIFMs, ManCos) News, Investment Firms News, Issuers of Tokens (EMTs, ARTs) News, Multimedia, Must Read, Opinion, Payment Institutions (PIs) / Electronic Money Institutions (EMIs) /AISPs News, Pension funds News, PFS/PSF News, Undertakings for collective investment (UCIs).
At https://Ratiofy.Lu/, we defend your hard-earned money with our free daily news platform and expert-vetted templates. Need more help? Request access to our hands-on expert Advisory, Training and Coaching Services (very limited availability) related to CSSF Circulars and EU Regulations.
The pre-filled example templates for many CSSF Circulars should be available at https://ratiofy.lu/templates/ from the summer of 2026.